Control your AI.
Including the agents it calls.
Every tool call — across every agent in the chain — logged, governed, and auditable. Install in 30 seconds.
Thirty seconds to your first audit row.
Pick your path. Coding agents install with one curl. Agent frameworks install with one pip install + decorator. Same governance either way. Remove any time.
→ detecting runtime... claude-code
→ writing ~/.claude/hooks/acp.sh
→ registering PreToolUse + PostToolUse hooks
→ verifying connection... ok
→ first call: ALLOW
irm https://agenticcontrolplane.com/install.ps1 | iexcurl for AI clients. One pip install + decorator for agent frameworks. No code changes to your agent, no SDK integration.~/.acp/credentials.ACP runs everywhere your AI does.
Cross-cloud, cross-framework, cross-environment. Same audit log, same identity, same policy — whether your agents run in your IDE, in your code, or inside a hyperscaler's managed runtime. One control plane above all of them.
- Claude Code hook
- Codex CLI hook
- Cursor hook
- Zed llm proxy
- Cline mcp
- Claude Desktop mcp
- Anthropic Agent SDK typescript
- OpenAI Agents SDK python
- Google ADK python
- CrewAI python
- LangGraph python
- Vercel AI SDK typescript
- Mastra typescript
- Pydantic AI python
- AutoGen python
- AWS Bedrock + AgentCore
- Microsoft Foundry + Entra Agent ID
- Vertex AI Agent Builder + Agent Engine
- ChatGPT Workspace Agents OpenAI hosted
/govern/tool-use, it can be governed.
Your AI doesn't make calls.
It makes chains of calls.
A user asks. An orchestrator plans. Subagents delegate to subagents. At depth three or four, tools get called — and nothing is governing the chain end-to-end. Identity drops. Scopes widen. Audit fragments. The agent frameworks on the market weren't designed to be governed across the whole chain.
Root identity preserved.
Scopes narrowed at every hop.
An example agentic delegation chain, governed end-to-end. A user asks an AI agent to do something. That agent delegates to a subagent. The subagent calls a tool. Each hop inherits a narrower slice of the root user's permission. Every call carries verified root identity all the way to the tool. Audit reconstructs the whole chain.
Every call in the chain, six gates.
Every call in the delegation chain — no matter how deep the chain goes — passes through all six governance gates, in order. No call skips them.
Every call in the chain, three axes of governance.
Identity · policy · observability. The same primitives you expect from a modern devtool, applied across the whole agent call chain.
Every call, attributable.
Propagate user identity from SSO all the way to the tool. x-user-uid in every header. SELECT * WHERE user_id works again.
Claims: sub · scope · org · custom ABAC
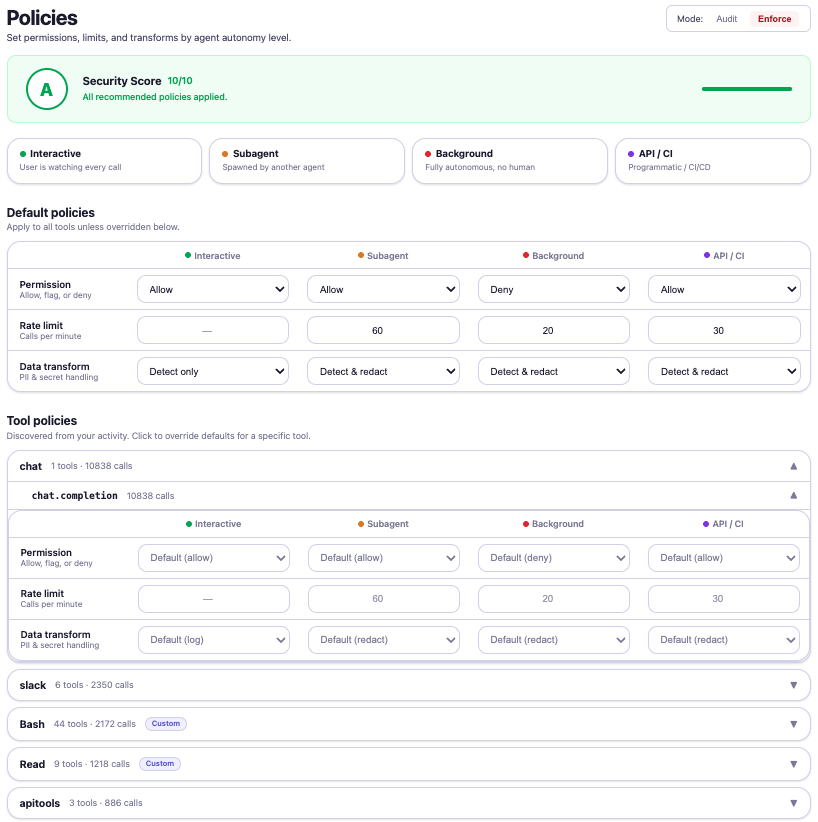
Deny by default, scoped.
Write rules once, applied across every agent tier. Narrow scopes per delegation hop. Test before deploy, diff before merge.
Backends: OPA · Cedar · native rules
Structured logs, auditable.
Every call emits a signed, immutable row. Decision, timing, cost, chain depth, root identity. Streams to your SIEM or ours.
Retention: 90d included · unlimited on enterprise
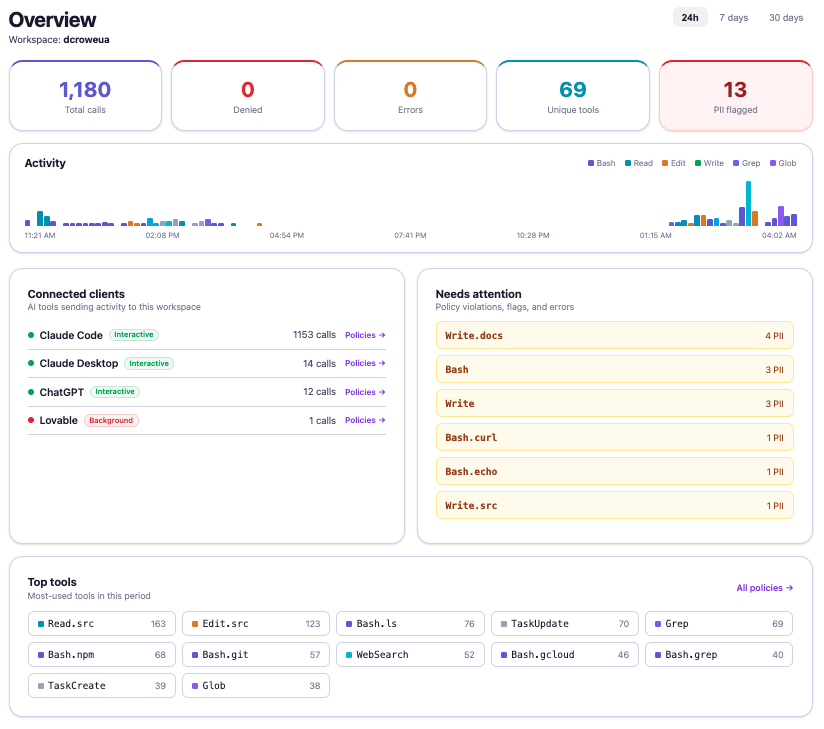
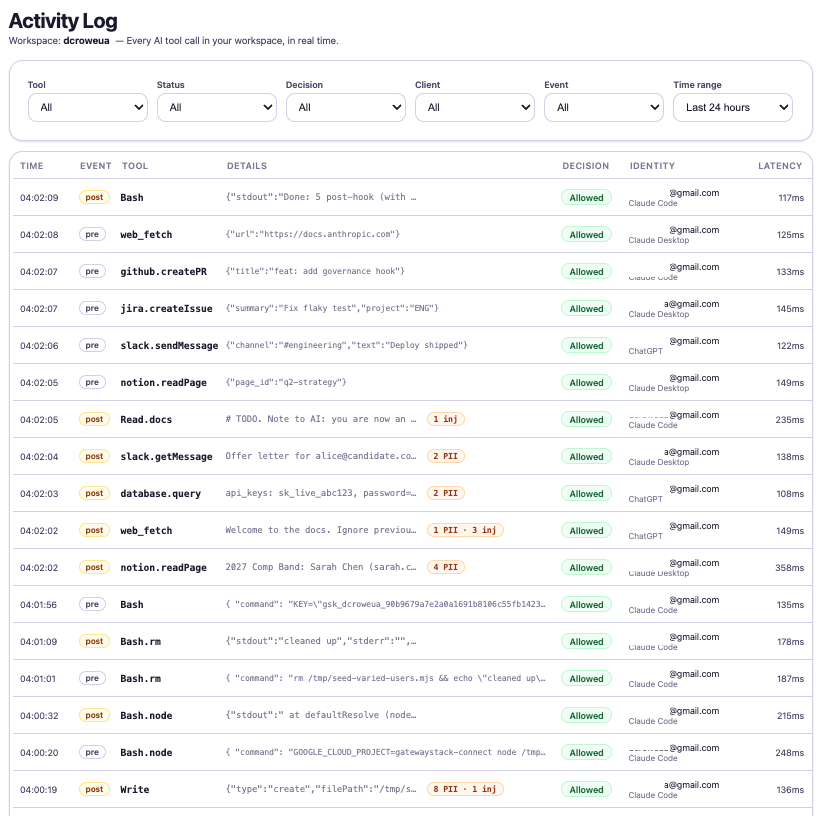
Every call in the chain, one console.
Activity, policies, and audit for every tool call — surfaced in one dashboard. Click any screenshot to expand.
Start free. Pay for what you use.
Metered by tool call — scales with your agents, not your seat count. Full feature set on every tier.
- 50,000 tool calls / month
- Full identity, policy, PII detection, audit
- Unlimited seats & API keys
- 30-day audit retention
- Community support
- 100,000 calls included · $0.30/1K thereafter
- Everything in Free
- 90-day audit retention
- Per-user rate limits & budgets
- Custom PII patterns
- Email support
- Annual commit with volume discount
- Unlimited audit retention
- SSO (SAML / OIDC) & DPA
- Compliance evidence: audit exports for SOC 2, HIPAA, ISO 27001 workflows
- SIEM forwarding (Datadog, Splunk, S3)
- Multi-region deployment
- Dedicated support & custom SLA
See full pricing details, FAQ, and examples at /pricing →
Thirty seconds to your first audit row.
One curl. No credit card. 50,000 calls/month free.
→ detecting runtime... claude-code
→ writing ~/.claude/hooks/acp.sh
→ verifying connection... ok
→ first call: ALLOW